Run the program without administrator rights and suppressing the UAC request
Many programs require elevation of rights at startup (the shield icon from the icon), but in fact for their normal operation, no administrator rights are required (for example, you manually give the necessary rights to users to the program directory in ProgramFiles and the registry branches that are used by the program). Accordingly, when launching such a program from a simple user, if UAC is enabled on the computer, a UAC prompt will appear and the user will be required to enter an administrator password. To get around this mechanism, many simply disable UAC or grant the user administrator rights on the computer, adding it to the local administrators group. Naturally, both of these methods are unsafe.
Why would a regular application need admin rights in Windows
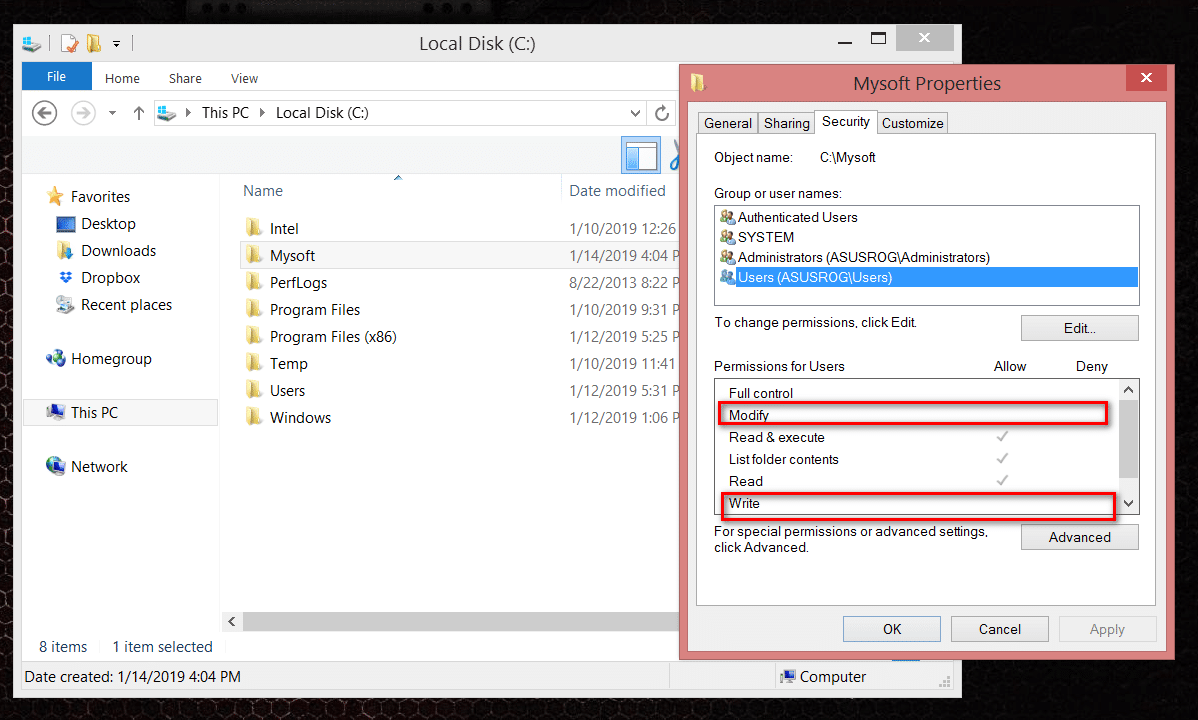
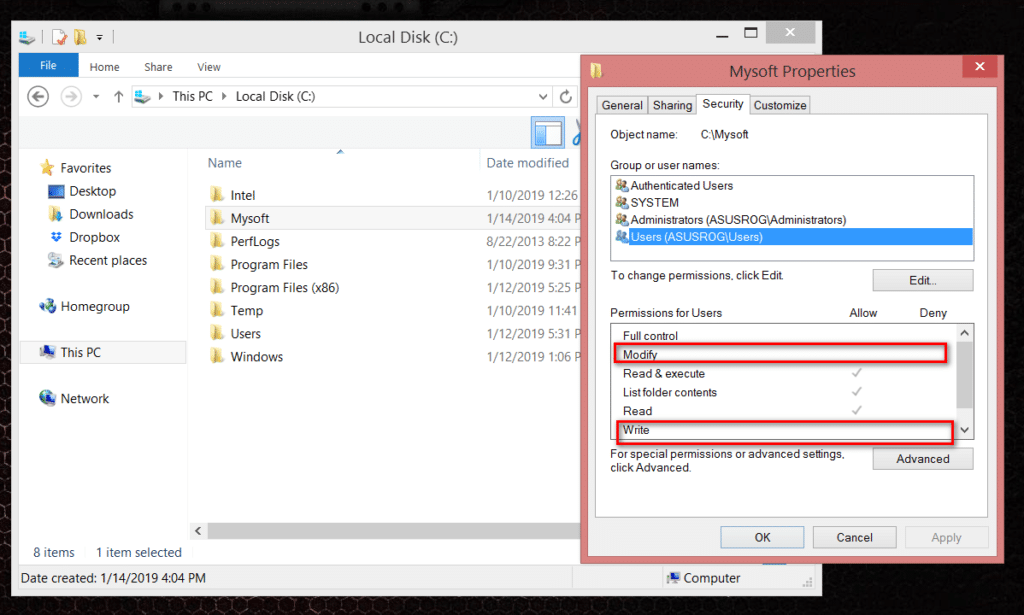
Administrator rights may be required for the program to modify certain files (logs, configurations, etc.) in its own folder in C: \ Program Files (x86) \ MyApp). By default, users do not have rights to edit this directory, respectively, for the normal operation of such a program, administrator rights are required. To solve this problem, you need to manually assign an edit / write permission for a user (or the Users group) to the program folder under the NTFS level administrator.
Note. In fact, the practice of storing changing application data in its own directory in C: \ Program Files is incorrect. It is more correct to store application data in the user profile. But this question is about the laziness and incompetence of the developers.
Run a program that requires administrative rights from a regular user
We have previously described how you can disable the UAC request for a specific program using the RunAsInvoker parameter. However, this method is not flexible enough. You can also use RunAs with saving admin / SAVECRED password (also unsafe). Consider a simpler way to force any program to run without administrator rights (and without entering the admin password) with UAC enabled (4.3 or 2 UAC slider level).
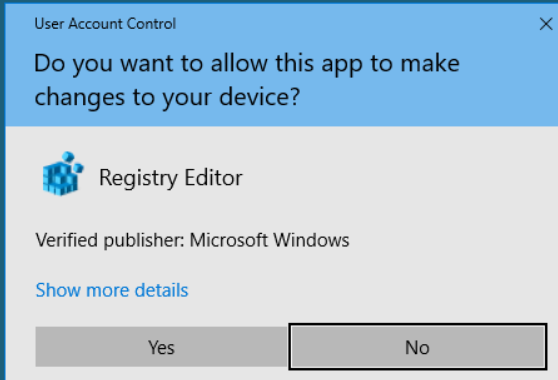
For example, let’s take the registry editing utility regedit.exe (it is located in the C: \ windows \ system32 directory). When you start regedit.exe, the UAC window appears and, if you do not confirm the privilege elevation, the registry editor does not start.
Create a run-as-non-admin.bat file on your desktop with the following text:
cmd / min / C “set __COMPAT_LAYER = RUNASINVOKER && start” “% 1”
Now, to force the application to run without administrator rights and suppress the UAC request, simply drag the required exe file onto this bat file on the desktop.
Similarly, you can run through the bat file and a specific application, it is enough to specify the path to the executable file.
run-app-as-non-admin.bat
Set ApplicationPath = “C: \ Program Files \ MyApp \ testapp.exe”
cmd / min / C “set __COMPAT_LAYER = RUNASINVOKER && start” “% ApplicationPath%”
You can also add a context menu that adds the ability to run without elevation for all applications. To do this, create the following reg file and import it into the registry.
Windows Registry Editor Version 5.00
[HKEY_CLASSES_ROOT \ * \ shell \ forcerunasinvoker]
@ = “Run as user without UAC elevation”
[HKEY_CLASSES_ROOT \ * \ shell \ forcerunasinvoker \ command]
@ = “cmd / min / C \” set __COMPAT_LAYER = RUNASINVOKER && start \ “\” \ “% 1 \” \ “”
After that, to launch any application without admin rights, just select the “Run as user without UAC elevation” item in the context menu.
The environment variable __COMPAT_LAYER and the RunAsInvoker parameter
The environment variable __COMPAT_LAYER allows you to set different compatibility levels for applications (the Compatibility tab in the properties of the exe file). Using this variable, you can specify the compatibility settings with which you want to run the program. For example, to run an application in compatibility mode with Windows 7 and a resolution of 640 × 480, set:
set __COMPAT_LAYER = Win7RTM 640×480
Most Of the interesting options for the variable __COMPAT_LAYER, we select the following parameters:
RunAsInvoker – launch application with the privileges of the parent process without asking UAC.
RunAsHighest – launch the application with the maximum rights available to the user (the UAC request appears if the user has administrator rights).
RunAsAdmin – start the application with administrator rights (AUC request always appears).
Those. the RunAsInvoker parameter does not provide administrator rights, but only blocks the appearance of the UAC window.